Unique ID System: Pros and Cons
On September 16, 2011, the Citizen’s Voluntary Initiative for the City and Centre for Advocacy and Research organized a public consultation titled “Unique ID System: Pros and Cons” in Bangalore. The consultation was on the utility and impact of the UID system in India and featured a panel discussion with T. Prabhakar, public relations officer, e-governance, Ashok Dalwai, UIDAI regional deputy director, Somashekar V.K., managing trustee of Grahak Shakti and Col. Mathew Thomas, civic activist and retired army officer.
Col. Mathew Thomas began his presentation by a comparative analysis of the Indian and the British experience in providing a unique identity to its citizens. In Britain, this initiative was labelled as ‘intrusive bullying’ and ‘an assault on personal liberties’. Additionally, the government recognized that they must conduct their business as servants of the public and not as their masters. The project was terminated on the grounds that it could not achieve the claimed objectives, and it was dangerous costly.
Nevertheless, the unique identification (UID) system in India is being perscribed as a prestigious project that will eliminate identity fraud, financial exclusion, enhance accessibility for the poor, enable the government to better manage welfare schemes and target corruption in social programs such as the National Rural Employment Guarantee Act (NREGA), the public distribution system (PDS), public health and financial inclusion.
Col. Mathew Thomas chronicled ID schemes. He explained that the advent and growth of information technology increased the availability of technology, which led to a commercial interest to exploit technology for profit. Technological solutions were heavily marketed, however, it is a mistaken belief that there is a technological fix to every problem (technology could solve any problem). Post 9/11 paranoia resulted in the notion that ID cards were the best possible counter measure to terrorism. “The inherent ridiculousness of this notion is that militants do not come with ID cards, but with AK-47s, and possession of ID cards or citizenship does not prevent one from becoming a terrorist”, says Mathew Thomas. National ID cards do not stop or deter terrorist actions.
India’s history with the UID project can be traced to the recommendations made by the Kargil Review Committee chaired by K. Subrahmanyam.The Committee recommended the issuing of ID cards to people in border areas to prevent infiltration and extend the system to the whole country to combat terrorism. Consequently, in 2003 the Citizenship Act of 1955 was amended by the NDA Government so as to compulsorily register all citizens into a “National Population Register” (NPR) and issue a Multi-purpose National Identity Card (MNIC). The NPR database will be inked to the UID. Subsequently, the UPA Government promoted the UID, as a pro-poor project.
Col. Mathew Thomas discussed the various questionable aspects of the UID project: its legality, financial prudence, ethics and its uses and abuses.
UID and Legality
Firstly, there is no law governing the functioning of the Unique Identification Authority of India (UIDAI). The illegal implementation of the UID is a complete insult to the Parliament and citizens, considering that the National Identification Authority of India Bill 2010 was drafted long after the implementation of the UID commenced.
UID and Financial Prudence
The high-level of apprehension surrounding the UID project stems from the fact that a project of this magnitude, cost and impact on the entire population would be undertaken without a feasibility study and a cost-benefit analysis. There exist two studies: one by the London School of Economics, regarding the UK project, and another by the Indian Institute of Management Ahmedabad, on UID in India. Both have concluded that such schemes are unworkable and too costly.
UID and Ethics
Ethical questions related to the UID are regarding its history, participation and ubiquity. Firstly, the UIDAI website is silent on the history prior to 2006. It fails to mention the significant historical roots of the UID, specifically, the Kargil War and the National Population Registry. Second, the UID has been promoted as a pro-poor project, whereas huge possibilities for commercial exploitation exist. Lastly, the UIDAI asserts that enrollment for the UID is ‘voluntary’. Although participation in the UID scheme is supposed to be voluntary, service providers can make it compulsory, thereby making it ubiquitous. A subtle campaign is being carried on, hinting at denial of benefits and services to those without UID.
Uses and Abuses
UID claims to transform governance, make ‘Bharath’ part of the growth process, plug ‘leakages’ & ‘slippages’ in welfare schemes, bring about all round prosperity and put India on a ‘fast-track’ growth by becoming the pivot around which all anti-poverty measures will rotate. One can conclude that UID is a panacea or a ‘one size fits all’ solution. Mathew Thomas questioned how these ambitions can be achieved by fingerprinting and scanning the irises of 1.2 billion people and storing the data for use by agencies responsible for the delivery of services.
These claims revolve around the assumptions that a lack of identity denies people welfare benefits; denies access to opportunities and services; and that a unique identification and de-duplication using biometrics would prevent “leakages”, “slippages” and in effect, all corruption. These assumptions need to be tested and verified so as to ensure validity.
The Public Distribution System and UID
Col. Mathew Thomas examined the PDS to analyze the use and claims of UID. He described the supply and demand of the PDS. The ‘supply’ side involves the fixing of minimum support prices, procurement by the centre and state governments, transport to FCI and state storages, distribution by centre to states and distribution by states to fair-price (ration) shops. All of the stages are affected by corruption and surprisingly UID beneficiaries have no role in any of the aforementioned stages.
‘Leakages’ in the supply process could potentially occur during the fixing of the minimum support prices (if deals exist with large farmers), during procurement (if they lift less quantity than what was paid for) and during accounting and storage (if they write off larger quantities than the actual damage; write off against bogus ration-cards; and show more quantity in storage and shops than is actually there).
The ‘demand’ process of the PDS system requires for state governments to decide on the eligibility of BPL people, issue ration cards, allocate ration-card holders to specific ration shops and requires the ration-card holders go to designated shops and collect entitlements. Corruption is possible, probable and happens in this discretionary decision-making. However, the only stage at which UID would find some use, if at all, is when ration-card holders collect rations.
Col. Mathew Thomas provided an excellent example of the government’s lopsided priorities. He describes the UID in PDS as the story of the ‘fence eating the corn’. The ‘fence’ then says, “let’s brand the cattle to find who is stealing the corn!”
The practicality of utilizing UID for authentication in the PDS system is a huge conundrum. Considering that the process to authenticate at ration shops requires all shops to have scanners (approximately six lakhs) which must be connected to a network and power at all the time.
Another problem surrounds the collection of ration. Ration-card holders do not always go to collect rations. There could be occasions where one family member goes for collection or one person collects rations for a number of families. The worst part of the UID application to the PDS system is that the procedure puts the BPL person at the mercy of the ration-shop keeper. He could simply deny rations, saying, “Authentication failed”.
The potential abuses of the UID could arise from the large collection of fingerprints that will be with various government officials and private agencies which could be used to foist false criminal cases against innocent people, forge title deeds, sale deeds, promissory notes wills, etc., and could target individuals and communities.
Col. Mathew Thomas concluded by explaining the main risks of any centralized database, it can be hacked and can crash. Professor Ian Angle, of the London School of Economics, has said that the UID will be "Olympic games of hacking", providing people with the biggest challenge to hack through.
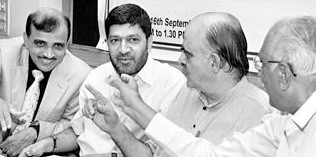
Making a point: (From left) Public Relations Officer, e-governance, T. Prabhakar; UIDAI Regional Deputy Director Ashok Dalwai; Managing Trustee of Grahak Shakti Somashekar V.K.; and civic activist Mathew Thomas at a panel discussion in Bangalore on Friday. — photo: V. Sreenivasa Murthy.
Photo Source: From the Hindu, September 17, 2011, http://goo.gl/gCnqK
Note: Unfortunately, the other presentations were conducted in Kannada and could not be understood by the author of this blog.


